child pornography
Top stories
[DIGEST: Motherboard, Engadget]
Back in February of 2015, the FBI infiltrated Playpen, a child pornography site on the Dark Web. But it did not shut down the site right away.
Instead, the agency continued to operate the site for nearly two weeks, distributing malware to its visitors in the hope of tracking and identifying suspected pedophiles around the world. The decision paid off: the FBI has successfully hacked more than 4,000 computers and charged 186 people as a result. But this week, Peter Adolf, an attorney for Steven Chase who is accused of running Playpen, argued in a motion to dismiss his client’s indictment that Playpen performed substantially better while under the FBI’s stewardship.
According to Adolf’s motion, the FBI “distributed child pornography to viewers and downloaders worldwide for nearly two weeks, until at least March 4, 2015, even working to improve the performance of the website beyond its original capability.” Adolf, an assistant federal defender in the Western District of North Carolina, alleges that Playpen experienced a 30 percent membership increase while under FBI control. The number of unique visitors also rose exponentially––from about 11,000 to 50,000 per week. Even more unsettling, Playpen distributed 200 videos, 9,000 images and 13,000 links to child pornography over the course of those two weeks.
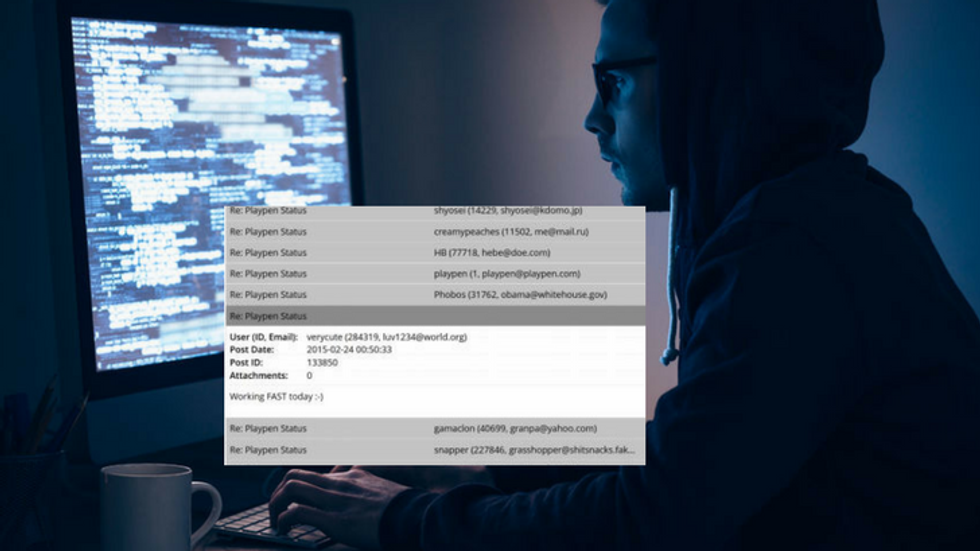
To support his claims, Adolf provided archived messages from Playpen users who complained about slow service and “server trouble” before the FBI took over. A message dated February 21, 2015 from Playpen user “verycute” mentions “having trouble getting in here all day” and “taking forever just to reply to this.” On February 23, someone in charge of a Playpen administrator account (Adolf alleges this was a member of the FBI) wrote back: “I upgraded the Token Ring [a type of network configuration] to Ethernet about an hour ago and things seem to be working a bit better.” Users were pleased with the change.

These improvements form the crux of Adolf’s argument: that the court should dismiss the charges against his client because
the FBI engaged in “outrageous conduct” by distributing child pornography on such a large scale. "Indeed, government agents worked hard to upgrade the website's capability to distribute large amounts of child pornography quickly and efficiently, resulting in more users receiving more child pornography faster than they ever did when the website was running 'illegally,'" Adolf wrote.
While Adolf is not the only attorney to question the FBI’s conduct––motions filed in related cases allege that the FBI distributed more than 1,000,000 images while operating Playpen––his motion is the first to claim that the FBI deliberately improved Playpen’s functionality to entice more users to join the website.
A spokesperson for the FBI declined to comment on matters pending litigation, and the FBI has moved to classify the hacking tool it used to infiltrate users' computers.
Government attorneys wrote that the FBI “derivatively classified portions of the tool… in accordance with the FBI's National Security Information Classification Guide” in a court filing made in response to a defendant in a related case. The FBI said “interests of national security” influenced its decision to classify the tool. In May, a federal judge ruled the government will not need to provide the browser exploit it used to alter Playpen users’ browser settings without their knowledge. The ruling dealt a major blow to defense teams who will likely be unable to examine how the FBI collected evidence against their clients.
 SECONDNEXUS
SECONDNEXUS percolately
percolately georgetakei
georgetakei comicsands
comicsands George's Reads
George's Reads